One of the benefits of being a Tesla owner is the convenience of the mobile app that allow you to control many functions of your vehicle from anywhere in the world. That convenience obviously has a lot of benefits, but there can also be some drawbacks.
These drawbacks come in the form of vulnerabilities, or a flaw or weakness in its design. One such vulnerability with Tesla’s mobile app was when you provide someone with access to your vehicle by adding them as a guest driver.
Fortunately Tesla has now fixed this particular vulnerability, which was discovered and reported by Ryan Levenson of The Kilowatts.
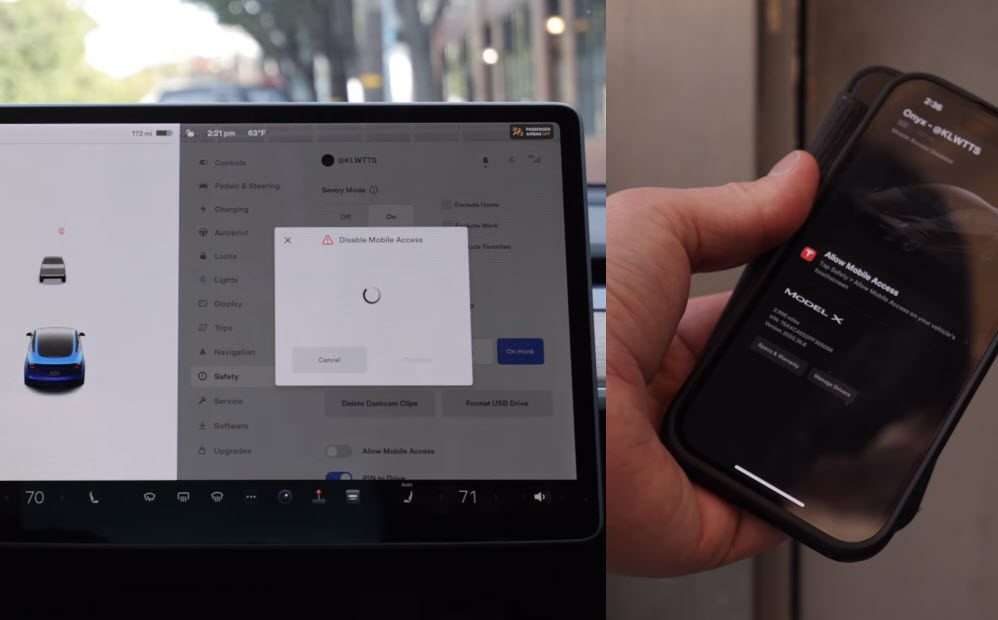
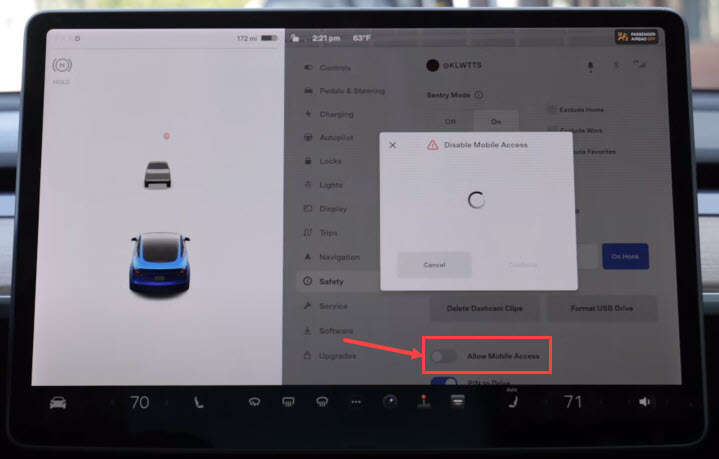
As a host on the car-sharing platform Turo, Levenson provided many of his guests with access to their rented vehicle through the “Add Driver” function in the mobile app. The problem was that these guest drivers could access all of the same controls on the in-car display, one of which was the command to disable mobile access.
This disabled mobile access for everyone that had an account linked to the car, including the owner, meaning the owner could no longer access the car in the mobile app to know its whereabouts.
Upon discovering this, Levenson tested it out on a number of other Tesla vehicles and confirmed it worked on all models with any software version, and that the owner received no notification their mobile access had been revoked. Tesla Service also confirmed they were not able to restore mobile access after it had been removed by another driver.
Showing off one of the benefits of having a connected vehicle like Tesla, Levenson reported the bug and it was fixed within one week. This particular bug was also fixed without the need for a software update as the changes were implemented on the server side.
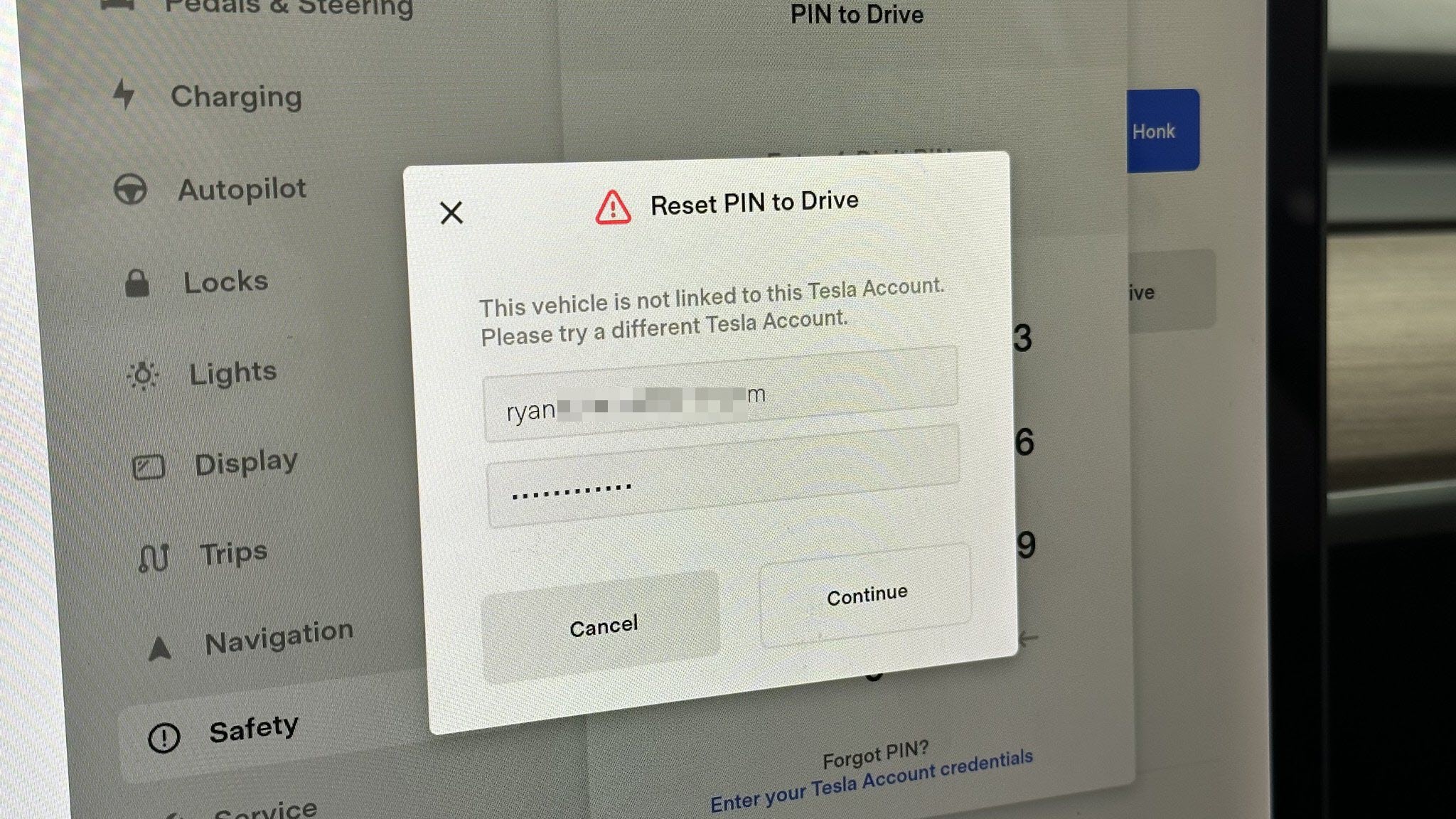
This vulnerability has been fixed by requiring the owner’s credentials to be entered before mobile access can be turned off. This level of security also extends to turning on PIN to Drive and setting up a PIN for glovebox access, which suffered from the same vulnerability.
Thanks to Tesla’s bug bounty program, Levenson was awarded $300 for reporting this vulnerability because Tesla considered this to be a P3 level of severity. The highest bug bounty is $15,000, but this was considered to be of a lower severity because it required physical access to the vehicle in order for it to be successful.
You can watch the full video from The Kilowatts which goes into more details below.

Always get the latest - make Drive Tesla your preferred source on Google
Are you buying a Tesla? If you enjoy our content and we helped in your decision, use our referral link to get three months of Full Self-Driving (FSD).