A security feature that is long overdue appears to be coming very soon as the option to add Multi-factor Authentication (MFA) has appeared on Tesla’s website.
Two-factor authentication is a common feature on almost all popular websites these days. For whatever reason the layer of security has been absent from Tesla accounts, despite the pleas from thousands of fans to have it added.
Tesla CEO Elon Musk has said as recently as August the feature would be coming soon, apologizing for it being “embarrassingly late.”
Sorry, this is embarrassingly late. Two factor authentication via sms or authenticator app is going through final validation right now.
— Elon Musk (@elonmusk) August 14, 2020
Thanks to keen-eyed Tesla fan @TeslaStraya, the feature appears to be just days away as a new section to add MFA has appeared in owner’s accounts.
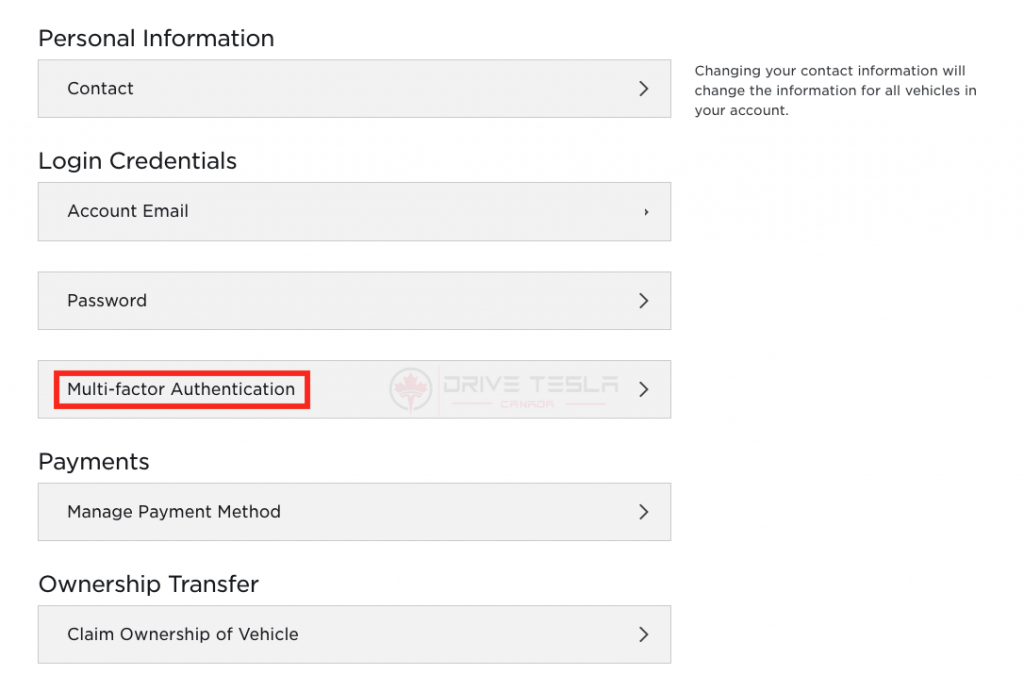
The option for MFA can be found by clicking on “Account” in the top right corner after logging in to your Tesla account.
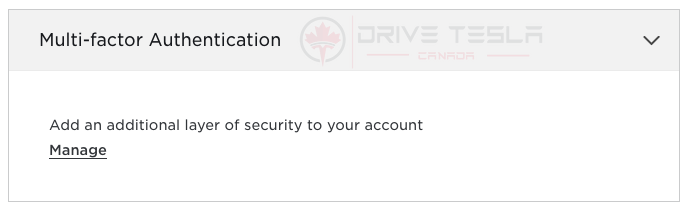
Under “Login Credentials” there is a new “Multi-factor Authentication” option which expands to allow the owner to manage the security feature. That link currently leads to a dead page mfa.tesla.com, but we suspect it will start functioning any time now.
We’ll be keeping an eye on the feature and let you know as soon as it’s available.
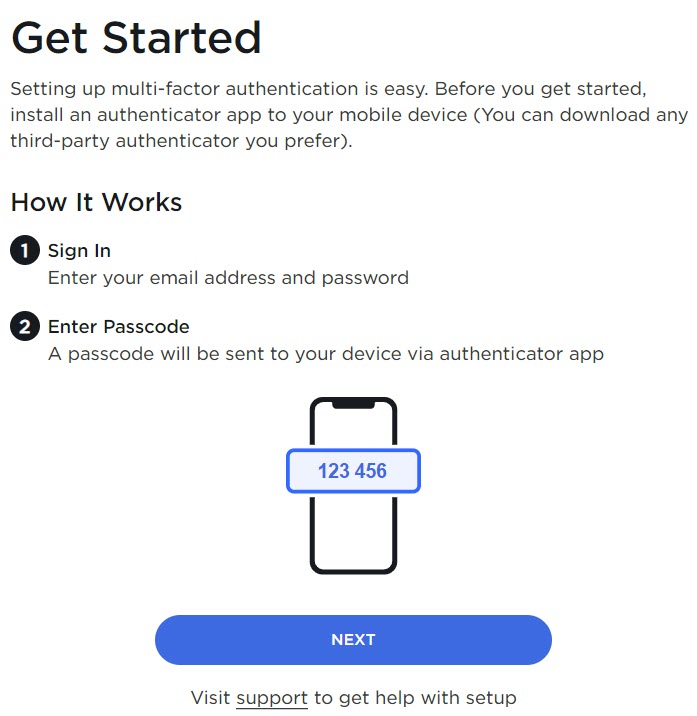
UPDATE October 6, 10:27am: Tesla has now activated the MFA option. Go visit your Tesla account and complete the steps to set it up.
What is two-factor authentication?
Two-factor authentication is an added layer of security for an account, beyond the typical username and password. In order to access the account, the user has to provide two pieces of “evidence” to prove you are the actual owner of the account.
This could be in the form of entering your password and then a code sent via SMS to your mobile device, or an additional security question.
The additional step to prove your identity is a great way to prevent someone from accessing your account without your authorization. While it is not 100% secure, it is much more difficult to hack and usually relies on social engineering tactics to learn the second layer of protection from the user.

Always get the latest - make Drive Tesla your preferred source on Google
Are you buying a Tesla? If you enjoy our content and we helped in your decision, use our referral link to get three months of Full Self-Driving (FSD).